The one cybersecurity mistake 90% of people make daily is overlooking the importance of proper email handling and not being cautious with links or attachments. Many click malicious links or share sensitive information because they fall for phishing attacks or aren’t aware of fake emails. This simple slip-up can lead to serious data breaches. Keep in mind, a small change in your daily habits can make a big difference—continue to learn how to protect yourself better.
Key Takeaways
- Most people frequently click malicious links or open suspicious emails, unknowingly exposing sensitive data.
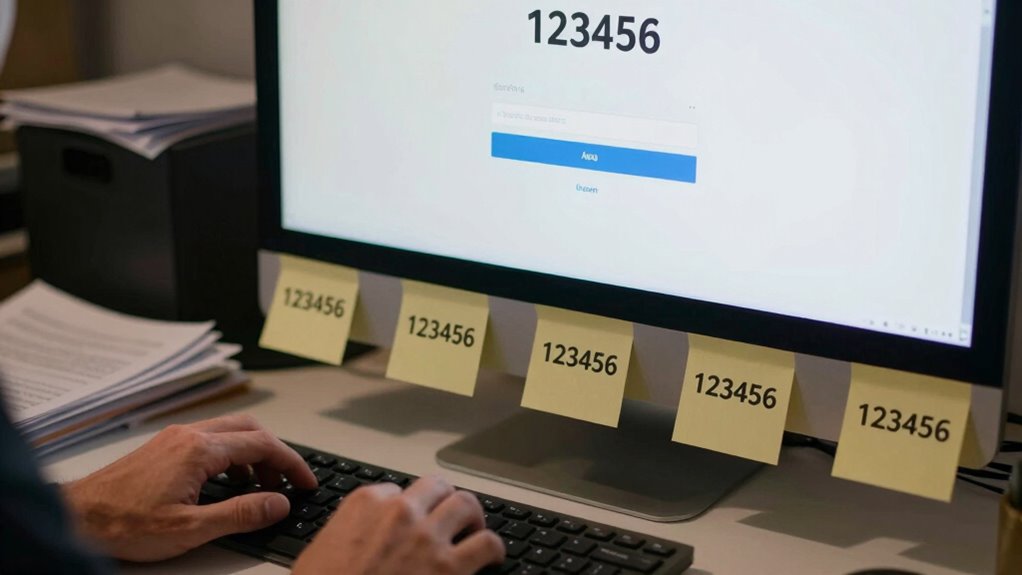
- Human errors like using weak or reused passwords are a common daily cybersecurity vulnerability.
- Employees often neglect routine software updates, leaving systems exposed to known vulnerabilities.
- Lack of cybersecurity awareness leads to mishandling emails and sharing confidential information.
- Daily slips such as misconfigurations or ignoring security protocols significantly increase breach risks.

Have you ever wondered why so many cybersecurity breaches happen despite advanced defenses? The answer often comes down to a single, repeated mistake that over 90% of people make daily: human error. No matter how sophisticated your security tools are, human actions still remain the weakest link. A staggering 88% of organizational data breaches result from employee mistakes, and recent studies confirm that human error contributes to 95% of data breaches overall. This isn’t just about malicious attacks; it’s about everyday slips that leave organizations vulnerable.
One of the most common mistakes is mishandling emails. Nearly half of all breaches involve employees sending personal information to the wrong recipient or falling for phishing scams. Phishing remains the most prevalent initial attack vector, responsible for over 16% of data breaches, with AI-driven phishing attacks increasing rapidly. Despite ongoing warnings, many employees still click on malicious links or provide sensitive information, often because they’re not adequately trained to spot these threats. It’s easy to become complacent when faced with convincing fake emails that look legitimate, especially when phishing attempts occur weekly or even daily for many organizations.
Weak password management is another critical issue. You might be using simple passwords like “123456” or reusing passwords across multiple accounts, which makes hacking straightforward. In fact, stolen credentials rank as the second most common attack vector, accounting for about 16% of breaches. When credentials are compromised, hackers can access corporate systems, especially if multi-factor authentication isn’t in place. Skipping MFA is a top mistake, leaving accounts vulnerable even if passwords are weak. Employees also often neglect to update passwords or rely on non-expiring credentials, giving hackers a long window to exploit these vulnerabilities.
Neglecting software updates and patches further compounds the problem. Outdated systems and unpatched vulnerabilities are prime targets for attackers. The 2017 Equifax breach, for example, happened because of an unpatched web application vulnerability. Many organizations ignore routine updates, leaving their defenses exposed. IoT devices, in particular, are often overlooked, with 70% of them vulnerable due to unaddressed risks. This neglect creates easy entry points for cybercriminals.
Your daily mistake might also involve a lack of proper training. Skimping on cybersecurity awareness leaves employees unprepared to recognize threats. Over 90% of hacked health records are stolen from unencrypted systems outside of electronic health records, illustrating the consequences of insufficient training and security protocols. When employees aren’t trained properly, they’re more likely to fall victim to phishing, mishandle sensitive data, or misconfigure security settings.
In essence, human error remains the most significant vulnerability in cybersecurity. No matter how advanced your defenses, if you don’t address this daily mistake—whether through training, better password practices, or vigilant email handling—you’re leaving the door wide open for attacks. Recognizing and correcting this fundamental flaw is your best chance at truly strengthening your security posture.
Amazon Product B0DKF4XH2Q
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Can Employees Recognize Phishing Attempts Effectively?
You can recognize phishing attempts by carefully inspecting email sender addresses for slight misspellings or unusual domains. Be wary of urgent language or requests for personal information, especially if unsolicited. Avoid clicking links or downloading attachments from unknown sources. Always verify suspicious messages through official channels. Trust your instincts—if something feels off, double-check before taking any action to prevent falling victim to scams.
What Are Simple Steps to Improve Password Security Daily?
You can improve your password security daily by creating strong, unique passwords for each account, avoiding common words or patterns. Use a reputable password manager to store and generate complex passwords automatically. Enable two-factor authentication whenever possible for added protection. Regularly update your passwords, especially after security breaches, and never reuse passwords across sites. Staying vigilant and disciplined with these habits dramatically reduces your risk of cyber threats.
How Often Should Software and Security Updates Be Applied?
You should apply software and security updates as soon as they’re available. Delaying updates leaves vulnerabilities open, increasing your risk of cyber attacks. Set automatic updates whenever possible, so your system stays protected without manual effort. Regularly check for updates if automatic options aren’t available. Staying current with patches and updates guarantees you’re closing security gaps promptly, reducing the chances of breaches caused by outdated software.
What Training Can Reduce Human Errors in Cybersecurity?
You can reduce human errors in cybersecurity by providing regular, hands-on training that covers common threats like phishing and password management. Encourage employees to stay updated on the latest security protocols and create clear procedures for reporting suspicious activity. Use simulated attacks to test their responses and reinforce good habits. By fostering a security-aware culture, you empower your team to recognize risks and act effectively, minimizing mistakes.
How to Identify Insider Threats Within an Organization?
Think of insider threats like a leak in your boat; you need to spot the signs early. You can identify them by monitoring unusual activity, such as accessing sensitive files outside normal hours or downloading large data volumes. Regularly review access logs, train staff to recognize risky behaviors, and implement strict access controls. Staying vigilant helps prevent small leaks from sinking your organization.

DEEPOWER QS7 Electric Bike for Adults, 2000W Peak Power 28MPH E-Bike, 48V 20Ah/35Ah/60Ah Battery Options, 35–180 Mile Range, 20” Fat Tire Ebike, 7-Speed All-Terrain Electric Bicycle
【High-Torque Electrified Thrills】 The Deepower electric motorcycle for adults delivers unmatched power with its Peak 2000W motor, reaching...
As an affiliate, we earn on qualifying purchases.
Conclusion
So, here’s the irony: despite knowing the risks, you probably still reuse passwords or click that suspicious link. It’s almost like you’re inviting hackers in, thinking it won’t happen to you. But in reality, that one small mistake could be all it takes to compromise everything. Maybe it’s time to break the cycle, stay vigilant, and outsmart those cybercriminals—because the biggest threat is often the one you ignore daily.

Gotrax R1 20" Folding Electric Bike with 40 Miles Range by 48V Battery, 20Mph Power by 350W, Weighs Only 45lbs, LCD Display & 5 Pedal-Assist Levels, Suitable for Leisure Riding&Commuting Black
【Powerful Riding Performance】Discover adventure with the GOTRAX R1 e-bike! Equipped with 20"*2.6" tires and a potent 48V battery,...
As an affiliate, we earn on qualifying purchases.

DTTZH F6 Peak 1500W Adult Electric Bike, Fast E Bikes for Adults Electric, 20" x 4" Fat Tire Ebike, 750W Motor Long Range Electric Mountain Bikes, 48V 15.6Ah UL 2849 Certified, 60 Miles Range (Black)
NFC UNLOCK & COLOR LCD DISPLAY - Forget bulky keys! Unlock the e-bike in 1 second via NFC...
As an affiliate, we earn on qualifying purchases.