DDoS attacks flood online services with excessive traffic from multiple sources, making it hard for legitimate users to access what’s needed. These attacks often use botnets, networks of compromised devices, to overwhelm websites, causing slowdowns or total unavailability. To combat this, organizations implement strategies like traffic analysis and filtering to protect their services. Understanding how these attacks work helps you appreciate the measures in place to keep services running smoothly, and there’s more to discover about their impact.
Key Takeaways
- DDoS attacks overwhelm online services by flooding them with excessive traffic from a network of compromised devices known as botnets.
- These attacks can lead to slow website performance or complete unavailability for legitimate users, disrupting normal service operations.
- Detection strategies involve analyzing traffic patterns to identify unusual behaviors and differentiate between genuine users and malicious bots.
- Organizations can mitigate DDoS attacks by investing in advanced security measures, traffic analysis tools, and adaptive response software.
- Understanding DDoS attack mechanisms enhances awareness of cyber threats and the importance of maintaining online service resilience.

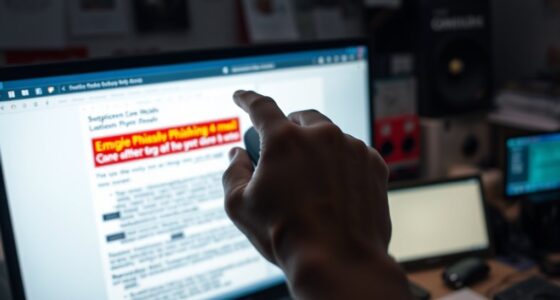
Have you ever wondered how a simple online service can suddenly become unreachable? It might feel like a glitch, but often, it’s the result of a Distributed Denial-of-Service (DDoS) attack. DDoS attacks overwhelm a service by flooding it with excessive traffic from numerous sources, making it impossible for legitimate users to access it. This malicious behavior typically involves a network of compromised devices, known as a botnet, which hackers control to release a torrent of requests.
When you’re on the receiving end of a DDoS attack, you might notice that your favorite website or service slows down considerably or becomes completely unavailable. This is because the servers handling the requests can’t keep up with the flood of data. The sheer volume of unwanted traffic consumes the bandwidth and processing power, effectively throttling the service’s ability to function properly. Bandwidth throttling can be a temporary solution for service providers to mitigate the effects of an attack, but it doesn’t eliminate the issue.
To combat these attacks, organizations employ various tactics, including botnet detection technologies. These systems analyze incoming traffic patterns to differentiate between legitimate users and malicious bots. By identifying unusual behaviors or spikes in traffic, they can quickly react to potential threats. The aim is to filter out the malicious traffic before it overwhelms the servers, allowing legitimate users to regain access. Detecting passive voice can enhance the effectiveness of these tactics by ensuring clear communication about traffic anomalies.
As a user, you may not see the behind-the-scenes efforts to fight against DDoS attacks, but they’re critical in maintaining service availability. Service providers invest heavily in security measures to protect their networks, including advanced software solutions that can quickly adapt to new forms of attack. Understanding the basics of DDoS attacks helps you appreciate the complexities involved in keeping online services operational.
Ultimately, while the internet offers incredible convenience, it’s also a battleground for cyber threats. Knowing how DDoS attacks work and the measures taken to prevent them can empower you to make informed choices about the services you use. So next time you encounter an unreachable service, you’ll have a better grasp of what might be happening behind the scenes, and you’ll appreciate the importance of botnet detection and bandwidth management in maintaining your online experience.

AED Defibrillator Cabinet with Alarm, Emergency Kit Box with Sirens and Flashing Lights for Home, School & Office
AED cabinets play a crucial role in the swift response to heart attacks. It is essential to place...
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
What Are the Different Types of DDOS Attacks?
There are several types of DDoS attacks you should know about. One common type involves traffic flooding, where attackers overwhelm your server with excessive requests. Another type uses botnet malware, which turns multiple compromised devices into a network that launches massive attacks. Additionally, application layer attacks target specific applications, making them unavailable. Recognizing these types can help you better prepare and protect your systems from potential threats.
How Can Businesses Mitigate DDOS Attacks Effectively?
To effectively mitigate DDoS attacks, you need a solid strategy. Start with robust network monitoring to detect unusual traffic patterns early. Invest in firewalls and anti-DDoS software to filter malicious requests. Don’t forget employee training; educating your team on security protocols and phishing threats helps build a strong defense. With these measures, you’ll fortify your business against potential disruptions—think of it as putting up a digital moat around your castle!
What Tools Are Available for DDOS Attack Protection?
For DDoS attack protection, you can use tools like web application firewalls (WAFs) and advanced firewall configurations to filter malicious traffic. Additionally, employing traffic analysis tools helps you monitor network behavior, identifying unusual patterns that may indicate an attack. Services from cloud providers often offer built-in DDoS mitigation features, which can automatically absorb and deflect harmful traffic. By combining these tools, you’ll strengthen your defenses against potential threats.
Are DDOS Attacks Illegal?
Yes, DDoS attacks are illegal. While some might argue they’re just a means of protest, the legal implications clearly state otherwise. You could face severe penalties, including fines and imprisonment. Ethical considerations also come into play; intentionally disrupting services harms innocent users and businesses. So, before you consider any action, think about the consequences. It’s not just about legality—it’s about making the right choice in a digital world.
How Can I Report a DDOS Attack?
To report a DDoS attack, start by documenting the attack details, including timestamps and symptoms. Contact your internet service provider (ISP) immediately; they can assist with attack detection and mitigation. You should also reach out to law enforcement, as they can guide you through the incident response process. Consider reporting the attack to cybersecurity organizations that track such incidents, as they can provide additional support and resources.

Wall-Mounted Steel AED Alarm Box, AED Defibrillator Storage Cabinets with Temperature Control System and Handle, -50-120℃ Range of Set Temperature, for Fits Most AED Models
【Wide Window】:Equipped with door handle and clear window for easy visual identification of the AED. Easy to use...
As an affiliate, we earn on qualifying purchases.
Conclusion
In a world where connectivity fuels progress, DDoS attacks threaten to bring it all crashing down. One moment, your online experience flows seamlessly; the next, it’s a frustrating standstill. Understanding these attacks isn’t just about protecting your network; it’s about safeguarding your digital future. By grasping the basics of denial-of-service, you empower yourself to stand against disruption, ensuring that the benefits of the internet continue to thrive amidst the chaos. Stay informed, stay secure!

Zoll AED Plus
The AED Plus automated defibrillator is simple to use. Its audio and visual prompts help BLS-trained responders rescue...
As an affiliate, we earn on qualifying purchases.
Amazon Product B0FL7HM5PM
As an affiliate, we earn on qualifying purchases.