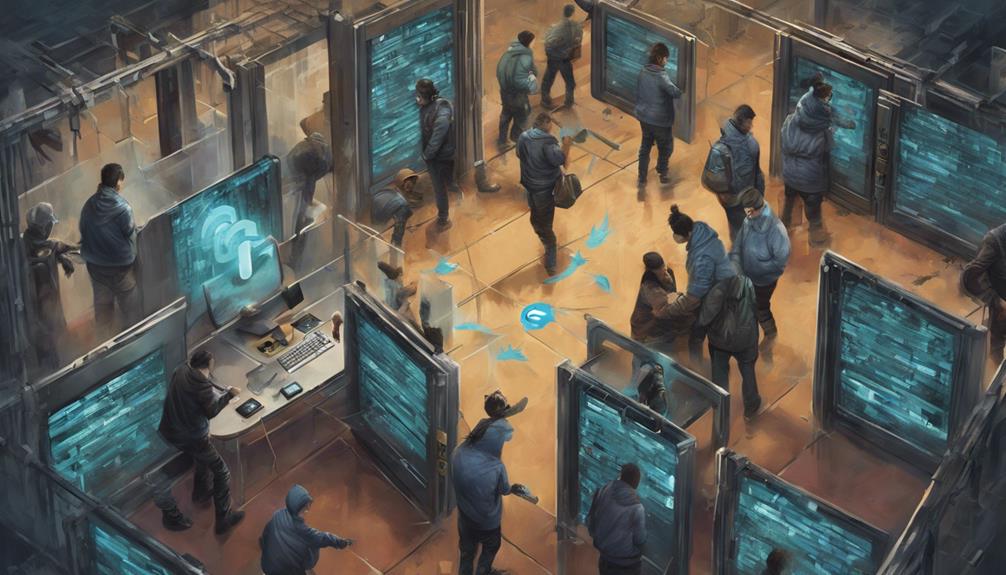
Mystified about Linux's security against hackers? Discover the robust measures that make it a challenging target.
Browsing Category
Cybersecurity Threats and Defense
288 posts
Is Cloud Storage Safe From Hackers
Uncover how cloud storage defends against hackers with robust encryption, authentication, and redundancy, ensuring data safety and integrity.
What Baby Monitors Are Safe From Hackers
Keen on protecting your baby's privacy? Discover which baby monitors are safe from hackers and how to keep them secure.
Is Whatsapp Safe From Hackers on Android
Not sure if WhatsApp on Android is safe from hackers? Explore the robust security measures that keep your communication secure.
Is Twitter Safe From Hackers
Faced with a history of security breaches, Twitter's vulnerability to hackers raises concerns, prompting a closer look at its safety measures.
Is Among Us Safe From Hackers
Gripping tales of hackers infiltrating Among Us gameplay reveal ongoing security challenges – but is the game truly safe?
Are Blink Cameras Safe From Hackers
Worried about the safety of your Blink cameras? Find out how recent vulnerabilities and security measures can impact your privacy.
Is Cryptocurrency Safe From Hackers
Uncover the truth about cryptocurrency's vulnerability to hackers and learn how to protect your digital assets with essential security measures.
Is Shopify Safe From Hackers
Discover how Shopify fortifies against hackers with robust security measures, encryption protocols, and proactive strategies, ensuring a safe platform for businesses.
Is the Nanit Safe From Hackers
Safeguarding your baby's data and privacy, discover how Nanit stays secure from hackers with advanced encryption and proactive monitoring.