Paying a ransom can seem like the quick fix during a ransomware attack, but it’s risky. Nearly half of organizations still pay, yet only about a quarter recover their data successfully, often at high costs. Paying can also fuel future attacks and doesn’t guarantee data recovery. Usually, better preparation and backups reduce the need for negotiations. If you’re interested, you’ll discover vital strategies to avoid costly ransom payments and protect your organization more effectively.
Key Takeaways
- Paying ransom often leads to repeated attacks and higher future costs, with 80% of organizations facing subsequent breaches.
- Negotiations can reduce ransom amounts, but there’s a risk of paying more than the initial demand or not recovering data.
- Ransom payments do not guarantee data recovery or protection from future cyberattacks.
- Strong backup and security strategies are more effective than paying ransoms to ensure quick recovery and resilience.
- Regulatory guidance generally advises against paying ransom due to ethical, legal, and financial risks.
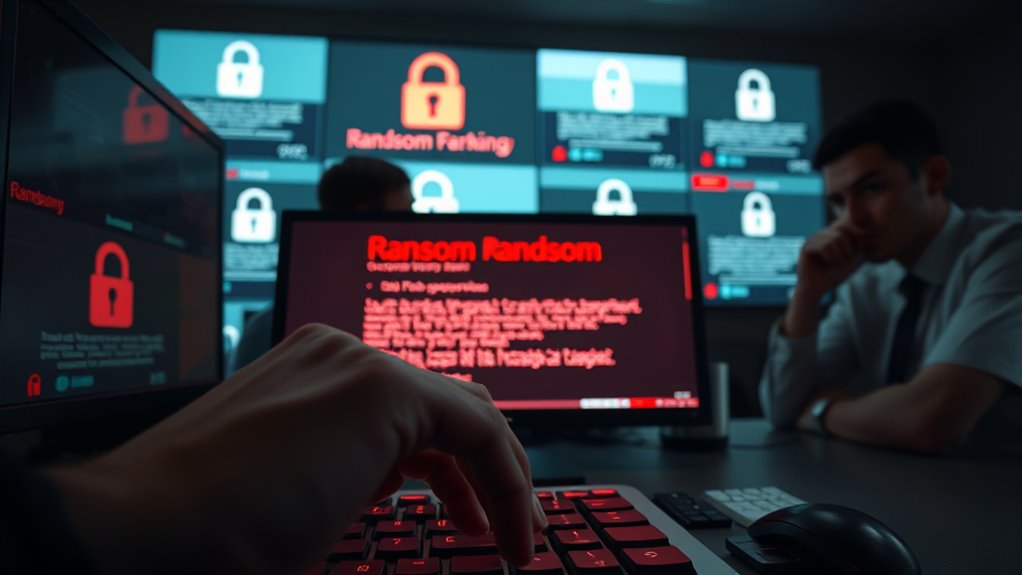
Have you ever wondered whether negotiating with ransomware attackers is worth the risk? It’s a common dilemma faced by organizations caught in a cyber crisis. On one hand, paying the ransom might seem like the fastest way to restore your data and resume operations. On the other, it fuels criminal activity, and there’s no guarantee you’ll get your data back or that the attackers won’t strike again. Recent trends show a complex picture. Ransom payments dropped 35% from $1.1 billion in 2023 to about $814 million in 2024, with the payment rate hitting a historic low of 25%. Despite this decline, nearly half of the companies still paid the ransom, marking the second-highest rate in six years. The median ransom amount has shrunk from $2 million in 2024 to $1 million in 2025, and the average recovery cost has also decreased considerably, from about $2.73 million to $1.53 million. Cyber insurance coverage often influences organizations to consider ransom payments as a viable solution. Negotiation outcomes reveal that over half of paying companies managed to lower their ransom, with 71% of these reductions achieved through direct negotiation or third-party negotiators. The median demand dropped by a third, and the actual payments halved between 2024 and 2025. However, the risks are stark. More than half of the targeted organizations, including schools and universities, found that they paid more than the initial demand—sometimes exceeding it—highlighting the unpredictability of negotiations. The average payment in late 2024 rose slightly, yet the median payment decreased sharply, indicating a wider variance in ransom demands. Recovery success rates are encouraging. Approximately 97% of organizations managed to retrieve their encrypted data, mainly through backups or, in some cases, payments. The time to full recovery has improved too, with 53% achieving it within a week and only 18% taking over a month. Better backup strategies and hardened security measures have contributed to a decline in encryption extortion. Still, the threat of repeat attacks remains high, with 80% of organizations that paid ransom experiencing another attack, often within a month and with higher demands. This cybercriminal behavior underscores the importance of comprehensive security measures. When contemplating whether to pay, consider the broader context. State and local governments tend to pay higher median amounts—around $2.5 million—while healthcare sectors report much lower figures. The financial toll can be severe, with many organizations suffering revenue losses and brand damage post-payment. Regulatory guidance increasingly advocates against paying ransom, emphasizing the importance of robust defenses and incident response plans. Negotiating can buy you time and sometimes reduce costs, but it’s a risky gamble that might not guarantee safety or data return. Ultimately, preparation, prevention, and expert guidance form the best strategy to avoid these costly and uncertain negotiations altogether.
Top picks for "ransomware negotiation should"
Open Amazon search results for this keyword.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
What Are the Legal Implications of Paying a Ransom?
Paying a ransom can have serious legal implications. You might inadvertently violate laws like the U.S. sanctions regulations, especially if the ransom goes to designated terrorist or criminal groups. You could also face charges related to funding illegal activities or violating export controls. Always consult legal experts before considering payment, as it can expose your organization to legal risks, penalties, and reputational damage.
How Does Paying Ransomware Affect Future Cyber Insurance Claims?
Paying ransomware can negatively impact your future cyber insurance claims. Insurers may see ransom payments as increased risk, leading to higher premiums or denied coverage altogether. They might also scrutinize your cybersecurity measures more closely afterward. If you pay, insurers could reduce or refuse to cover related recovery costs or damages, making it harder to recover financially. To protect your coverage, consider strengthening defenses and avoid paying ransom unless absolutely necessary.
Can Paying Ransom Increase the Likelihood of Repeat Attacks?
Paying ransom can increase your chances of facing repeat attacks, as 80% of organizations that pay end up targeted again. Attackers view payments as a sign of vulnerability, encouraging them to strike multiple times. Additionally, 68% of these repeat attacks happen within a month, with higher demands. So, by paying, you might inadvertently signal weakness, making your organization a repeated target for cybercriminals.
Are There Effective Non-Monetary Ways to Negotiate With Attackers?
Yes, there are effective non-monetary ways to negotiate with attackers. You can focus on demonstrating compliance with their demands without paying, such as providing proof of backups or security measures. Engage cybersecurity experts to communicate with attackers to buy time or negotiate reduced demands. Additionally, reporting the incident to authorities can sometimes lead to legal or technical assistance, discouraging further threats or attacks. Always prioritize your organization’s safety and legal guidance.
How Do Industry-Specific Risks Influence Negotiation Strategies?
Like a chess master anticipating moves, your negotiation strategy must adapt to industry risks. In healthcare, where data breaches threaten patient safety, you might prioritize quick recovery over payment, while in government sectors, legal and regulatory risks push you to avoid negotiations altogether. Knowing each industry’s vulnerabilities helps you craft smarter strategies, balancing risk and recovery, so you can make informed decisions rather than reacting impulsively.
Conclusion
So, next time you’re faced with a ransomware attack, remember: paying the ransom isn’t a clear-cut choice. Will surrendering your data truly save your business, or does it open the door to future threats? The decision hangs in the balance, and one wrong move could cost you more than you imagine. Stay vigilant, weigh your options carefully, and never underestimate the unpredictable outcome of negotiating with cybercriminals. The stakes have never been higher.