Social engineering is tough to defend against because it exploits human psychology, trust, and emotions rather than technical flaws. Attackers prey on natural tendencies like helpfulness, curiosity, and fear by creating convincing scenarios that feel familiar. Because humans are inherently trusting, it’s difficult to distinguish between legitimate and malicious interactions. Their tactics adapt dynamically, personalizing approaches using social media info, making defenses complex. Stay with us to uncover how understanding these psychological tricks can help keep you safer.
Key Takeaways
- It exploits natural human emotions like trust, fear, and curiosity, making individuals more susceptible to manipulation.
- Personalization through social media and tailored tactics increase convincingness and reduce suspicion.
- The human element often bypasses technical defenses, relying on psychological influence rather than technical vulnerabilities.
- Insider threats leverage existing trust and access, complicating detection and prevention efforts.
- Continuous adaptation and evolving tactics by attackers require ongoing vigilance, training, and skepticism.

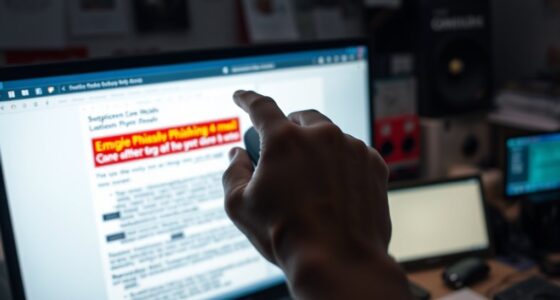
Have you ever wondered how easily attackers can manipulate employees into revealing sensitive information? Social engineering exploits psychological manipulation to bypass even the most advanced security measures. Attackers craft convincing scenarios that prey on human emotions—trust, fear, curiosity—to persuade you to act against your best interests. Unlike technical defenses, which can be tested and fortified, social engineering targets the human element, making it uniquely challenging to defend against. This persistent vulnerability is what makes social engineering so difficult to combat effectively.
Social engineering exploits human emotions to bypass security, making it a uniquely challenging and persistent threat.
One reason it’s so hard to defend against social engineering is that it plays on natural psychological tendencies. Humans are inherently trusting and eager to help, especially when approached confidently and convincingly. Attackers often impersonate colleagues, IT support, or even executives, creating a sense of familiarity that lowers your guard. They understand that your instinct to be helpful or avoid conflict can override your rational assessment of a suspicious request. This psychological manipulation makes it difficult to distinguish between legitimate and malicious interactions, even for seasoned employees. Recognizing how human psychology can be exploited is essential for developing effective defenses. Additionally, attackers often adapt their tactics based on the responses they observe, making each attempt more convincing than the last.
Insider threats further complicate the landscape. Employees with access to sensitive information might be coerced, manipulated, or even unwittingly recruited into malicious schemes. When someone inside the organization is compromised or acts maliciously, the breach becomes more dangerous because the attacker already has a level of trust and access that external hackers lack. Protecting against insider threats requires more than just technical controls; it demands more human vigilance and awareness of human vulnerabilities. Since social engineering often involves manipulating these insiders, organizations must foster a culture of skepticism and security consciousness to mitigate these risks. Furthermore, the personalized nature of social engineering tactics increases the challenge, requiring continuous education and awareness initiatives.
What makes social engineering particularly insidious is its adaptability. Attackers constantly refine their tactics based on their target’s responses, making each attempt more convincing than the last. They may use information gathered from social media to personalize their approach, increasing the likelihood that you’ll believe their story. This personalized approach taps into your desire to be helpful or to comply, making it harder to resist. Because of these dynamic strategies, traditional cybersecurity measures alone aren’t enough. You need ongoing training, awareness, and a healthy dose of skepticism to recognize and thwart social engineering attempts.
In essence, social engineering’s success hinges on exploiting human psychology and insider threats, making it an ongoing challenge for organizations. Defending against it requires understanding these vulnerabilities deeply and constantly adapting your defenses. It’s a game of psychological resilience, where staying alert and questioning suspicious interactions is your best weapon. Recognizing the importance of biographies and entertainment content can also help organizations foster a well-informed and vigilant workforce. Developing a comprehensive understanding of human behavior is crucial to building effective defenses against social engineering attacks.
phishing awareness training courses
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Do Attackers Craft Convincing Social Engineering Messages?
Attackers craft convincing social engineering messages by researching their targets and mimicking trusted sources. They use tactics like phishing simulations to test employees’ responses and identify vulnerabilities. Through personalized details and urgent language, they create a sense of legitimacy. Effective employee training helps you recognize these tactics, but attackers constantly adapt, making it challenging to defend against sophisticated, believable messages. Staying vigilant and informed is your best defense.
What Psychological Tactics Are Most Effective in Social Engineering?
You find that psychological manipulation and emotional appeals are most effective in social engineering because they tap into your feelings and instincts. Attackers often create a sense of urgency or fear, making you less likely to think critically. They might pretend to be someone trustworthy or share relatable stories to build rapport. By appealing to your emotions, they increase the chances you’ll act impulsively, revealing sensitive information or granting access.
Can Machine Learning Detect Social Engineering Attacks?
Yes, machine learning can detect social engineering attacks through automated detection and behavioral analysis. It analyzes patterns in communication and user behavior to spot suspicious activity. By learning from past attacks, it identifies anomalies that might indicate social engineering attempts. This proactive approach helps you catch threats early, reducing the risk of successful attacks. While not perfect, combining machine learning with other security measures strengthens your defenses against social engineering.
How Do Cultural Differences Impact Social Engineering Tactics?
Cultural differences are like a maze, making it tricky to spot social engineering attacks. You might fall for a scam because of cultural nuances or language barriers that mask malicious intent. Tactics vary based on local customs, beliefs, and communication styles, which can confuse you or make you more trusting. Recognizing these subtle cues and understanding cultural context helps you defend against manipulative tricks tailored to specific audiences.
What Are the Signs of a Social Engineering Attempt?
You can spot a social engineering attempt through signs of user deception and trust exploitation. Be wary of unexpected emails, urgent requests, or messages asking for sensitive information. Watch for inconsistencies in the sender’s details or tone that seem off. If someone pressures you to act quickly or bypass security protocols, it’s likely a scam. Trust your instincts and verify identities before responding to any suspicious communication.

Social Engineering: The Science of Human Hacking
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
You now know that social engineering isn’t just tricky—it’s an unstoppable force that can outwit even the most vigilant defenses. It’s like trying to stop a hurricane with a paper umbrella! But don’t despair; awareness is your secret weapon. Stay alert, question every request, and never let your guard down. Because if you think you’re safe today, social engineers are already plotting their next mind-bending attack. Stay sharp—your security depends on it!

ComplyRight OSHA All-in-One-Safety Poster with GHS Updates- Employee Information Poster
INFORMATIVE: The ComplyRight OSHA All-In-One-Safety Poster will help ensure that companies keep all employees up-to-date on OSHA and…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Mobile Application Development, Usability, and Security (Advances in Multimedia and Interactive Technologies)
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.