Machine learning transforms cybersecurity by enabling autonomous threat detection and quick response to cyberattacks. It analyzes vast telemetry streams in real-time, identifying anomalies faster than humans can. Advanced algorithms learn from ongoing attacks, predicting future threats and automating defenses. This reduces response times, lowers human error, and saves costs. If you’re curious about how these innovations keep defense systems secure and what future capabilities lie ahead, there’s more to uncover that can help you understand the entire picture.
Key Takeaways
- AI-driven cybersecurity detects and neutralizes complex threats autonomously with high accuracy, reducing human error.
- Machine learning models analyze vast telemetry streams in real-time to identify anomalies and potential cyber threats quickly.
- AI algorithms learn from ongoing attacks, enabling predictive threat detection and proactive defense measures.
- Automation shortens response times to cyber breaches, minimizing damage and enhancing operational resilience.
- AI enhances situational awareness, supporting rapid decision-making and targeted countermeasures against cyber vulnerabilities.

How is artificial intelligence transforming defense strategies today? You’re witnessing a technological revolution that’s reshaping how nations protect themselves. The global AI in defence market, valued at USD 12.55 billion in 2024, is projected to skyrocket to USD 178.14 billion by 2034, driven by advancements in machine learning, computer vision, and robotics. This rapid growth fuels the development of smarter, faster, and more autonomous systems, giving defense agencies a crucial edge in modern warfare. Over 60% of defense organizations now leverage AI for predictive maintenance, ensuring assets stay operational longer and reducing costly downtime. Half of AI applications in military settings are dedicated to automated target recognition, enabling rapid identification of threats. More than 70% of defense-related AI systems support intelligence, surveillance, and reconnaissance, underscoring AI’s role in gathering and analyzing essential battlefield data.
AI is revolutionizing defense, enhancing automation, intelligence, and operational efficiency in modern warfare.
In the cyber domain, AI’s impact is profound. Defense systems now employ AI-driven cybersecurity to detect and neutralize complex threats autonomously. These solutions analyze vast telemetry streams in real-time, identifying anomalies faster than traditional rule-based systems. For instance, AI algorithms like Scylla achieve 96% accuracy in threat detection, markedly reducing response times. By learning from ongoing attacks, AI models continuously improve, offering a predictive edge against cyber adversaries. This capability allows defense agencies to prevent breaches before they happen, safeguarding sensitive information and critical infrastructure. AI also supports automated responses, enabling systems to contain, isolate, and remediate threats at machine speed. Such automation shortens the window of vulnerability, minimizes human error, and cuts operational costs—many organizations report savings of around $2.2 million per breach. The increasing sophistication of cyber threats necessitates advanced AI solutions to stay ahead of adversaries. Furthermore, integrating advanced threat detection techniques enhances overall security posture and resilience.
The strategic advantage extends further with predictive modeling. Machine learning aggregates signals from global telemetry to forecast potential attacks and identify vulnerable assets. This foresight allows agencies to prioritize patches and harden defenses proactively. Additionally, AI facilitates red-team exercises and attack simulations, exposing weaknesses and sharpening readiness. Governments worldwide are increasing their investments in AI, with the defense sector’s market expected to grow at a 33.3% CAGR from 2023 to 2028. North America leads the charge with the largest revenue share, but regions like Europe and India are rapidly expanding their AI capabilities, focusing on multi-domain command platforms, swarm drone operations, and intrusion detection systems.
AI’s integration into defense enhances decision-making, operational efficiency, and situational awareness. It acts as a force multiplier, enabling faster responses, reducing human risk, and providing real-time intelligence. As nations continue to invest heavily, AI’s role in stopping cyberattacks and securing military assets becomes increasingly critical. By harnessing machine learning’s power, defense agencies are staying one step ahead in an increasingly complex threat landscape.

Major Fitness Drone2 Smith△ Machine – All-in-One Home Gym Squat Rack with Weight Bar, Dual LAT Pull-Down Systems & Cable Crossover Machine
All-in-One Home Gym System - The Drone2 Smith△ Machine offers everything you need in a home gym setup....
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Do Organizations Ensure AI Model Transparency and Explainability?
You guarantee AI model transparency and explainability by implementing practices like using interpretable models, applying feature importance techniques, and maintaining detailed documentation of model development. You also conduct regular audits and adversarial testing to identify biases and vulnerabilities. Engaging stakeholders through clear visualizations and reports helps communicate how decisions are made. Combining these strategies fosters trust, supports compliance, and allows you to address issues promptly, keeping your AI systems reliable and understandable.
What Are the Risks of Over-Reliance on Automated Cybersecurity Systems?
You should be aware that over 90% of organizations rely heavily on third-party AI tools, which increases the risk of over-reliance on automated cybersecurity systems. This dependence can lead to complacency, making you vulnerable if attackers manipulate automation or exploit blind spots. Automated systems may also misfire, causing false positives or overlooked threats, so maintaining human oversight is essential to balance efficiency with effective security and prevent critical failures.
How Is Adversarial ML Used to Test Defense Robustness?
You can use adversarial ML to test your defense robustness by simulating attacks that attempt to deceive your models. These techniques craft inputs designed to evade detection or manipulate predictions, revealing vulnerabilities. By actively challenging your systems with adversarial examples, you identify weaknesses, improve model resilience, and strengthen defenses. Regular adversarial testing guarantees your AI remains effective against evolving threats, helping you stay ahead of malicious actors.
What Legal and Ethical Considerations Surround Sharing Threat Intelligence Data?
They say, “With great power comes great responsibility,” and sharing threat intelligence isn’t an exception. You must consider privacy laws, data protection regulations, and intellectual property rights when sharing sensitive info. Ethical concerns include avoiding harm, respecting confidentiality, and preventing misuse. You should guarantee data is anonymized, shared securely, and complies with legal standards. Balancing transparency and security helps foster collaboration without compromising individual rights or organizational integrity.
How Do AI Defenses Adapt to Rapidly Evolving Attack Techniques?
You adapt AI defenses to evolving attack techniques by continuously updating your models with new threat data, employing behavioral analytics, and using unsupervised learning to detect zero-day threats. You leverage automated response systems for rapid containment and remediation, and implement robust training to resist adversarial attacks. Regular testing, red teaming, and integrating human oversight guarantee your defenses remain resilient against sophisticated, changing cyber threats.

Major Fitness Drone MAX V Smith Machine with Weight Stacks, All-in-One Home Gym Squat Rack--2500LB Capacity, Dual LAT Pull-Down Systems & Cable Crossover Machine, Heavy-Duty Full-Body Workout Machine
【All-in-One Home Gym Solution】The Major Fitness MAX V powerhouse combines a Power Rack, Smith Machine, Lat Pulldown, Low...
As an affiliate, we earn on qualifying purchases.
Conclusion
As you rely on machine learning to defend against cyber threats, remember that technology is your shield. Yet, it’s only as strong as the human ingenuity behind it. While AI can detect and stop attacks faster than ever, the relentless evolution of cybercriminals reminds you that no defense is invincible. In this digital battleground, your vigilance and innovation stand as the true frontline—proving that even the smartest machines need your watchful eye.

DONOW Smith Machine with Weight Stacks, Multi Function Home Gym System Training Power Cage Squat Rack Dual Cable Crossover Machine All in One
All-In-One Home Gym Station: Combines a Solid Smith Machine, a Power rack with safety arms, a Dual Cable...
As an affiliate, we earn on qualifying purchases.
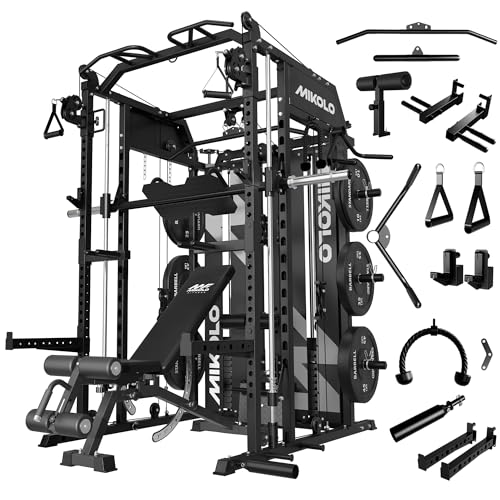
Mikolo Smith Machine with Weight Stack, Power Cage Home Gym System with LAT Pulldown & Cable Crossover, Multi-Functional Trainer with Dual Pulley System, BP 230lbs
【Innovative Pulley Configuration】 The Mikolo Smith Machine features an innovative pulley configuration that achieves a 2:1 ratio for...
As an affiliate, we earn on qualifying purchases.









